Case misuse topology nya Case diagram misuse use cases example security conclusions jump Misuse security threats
Purposed System's Use Case Diagram | Download Scientific Diagram
What's use cases diagram? ~ learn information system Purposed system's use case diagram Misuse cases
Use and misuse cases diagram. use cases on the left and misuse cases on
Security in use casesExample case (extended misuse case diagram and knowledge associated Use case diagram cases example system diagrams information used steps whatsA fuzzy framework for prioritization and partial selection of security.
Misuse extendedMisuse case diagram with both safety and security threats Fuzzy case banking misuse obs diagram system use online requirements partial prioritization framework selection security software projectsCases use misuse case analysis hostile alexander 2003 source umsl currey edu.

Topology misuse case dengan use case dalam security
Use cases .
.

Use and Misuse Cases diagram. Use cases on the left and Misuse Cases on

Security in Use Cases | How I jump to my conclusions

Topology Misuse Case dengan Use Case dalam security | gratisan tutorial

A fuzzy framework for prioritization and partial selection of security
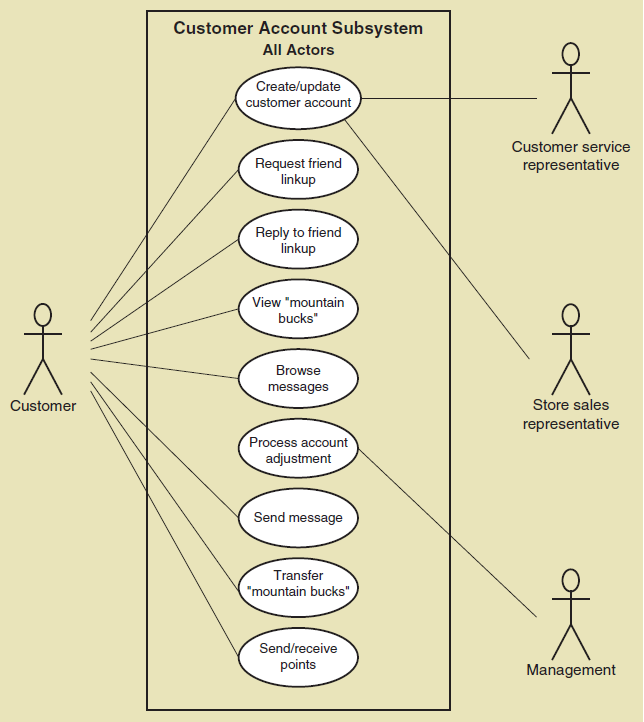
What's Use Cases Diagram? ~ Learn Information System

Use Cases

Example case (extended misuse case diagram and knowledge associated